Digital evidence can strengthen a case or destroy it. Courts rely on precision, not assumptions. Even small errors, like a mislabeled file or an overwritten log, can cast doubt on authenticity.
So legal teams must treat digital artifacts with the same care as physical evidence, applying consistent procedures and documented handling to preserve trust in every byte. Here’s an overview of the main errors to watch for.
Breaking the Chain of Custody in Digital Evidence
Breaking the chain of custody means the documented path of digital evidence gets interrupted. When files move between devices or investigators without full tracking, defense teams can challenge authenticity. Even renaming a folder or transferring data without timestamps can raise doubts about integrity.
Courts view such breaks as red flags and sometimes dismiss the evidence altogether. Maintaining a verified chain, with signatures and access logs, keeps each handoff transparent.
Working with an expert who’s well-versed in these processes, as well as how they apply locally, is a must. For instance, a professional defense attorney for criminal cases in Friendswood can take the reins when it comes to documenting every movement, labeling media precisely, and using verified forensic tools. Their oversight ensures that digital records withstand scrutiny and remain admissible.
Altering or Misinterpreting Timestamps
Altering or misreading timestamps can flip the timeline of a case. System clocks drift, time zones confuse records, and copied files may inherit new metadata. When investigators skip verification, events appear out of order, weakening the narrative.
Courts expect proof that digital times match real-world actions. So forensic analysts must compare device clocks with network or server logs and preserve the original time data. Accurate timestamps tell the story clearly, showing what happened and when, without leaving room for doubt.
The Risk of Relying on Screenshots as Primary Proof
Screenshots look convincing but rarely hold up as primary evidence. They capture what appears on a screen, not the data’s true source. Anyone can crop, edit, or fabricate them within minutes.
Judges prefer original digital files, complete with metadata, logs, and verification hashes. A screenshot should serve only as a visual reference, never the foundation of proof. Collecting the raw data behind the image and confirming its origin through forensic validation ensures the record remains credible and defensible under examination.
Mishandling Cloud Service Logs During Discovery
Cloud logs often contain crucial clues, but mishandling them can erase accountability. Many services automatically rotate or delete logs, leaving gaps in activity records. When legal teams delay collection, evidence may vanish before preservation orders take effect.
Proper handling means requesting data directly from providers, maintaining verified export records, and documenting retention settings. Analysts should capture logs in native formats and store them in tamper-evident systems. Precise coordination between counsel and IT ensures that cloud evidence remains complete, traceable, and admissible in court. This could even be a factor to consider when choosing between cloud storage options.
Overlooking Mobile Backups and App Data
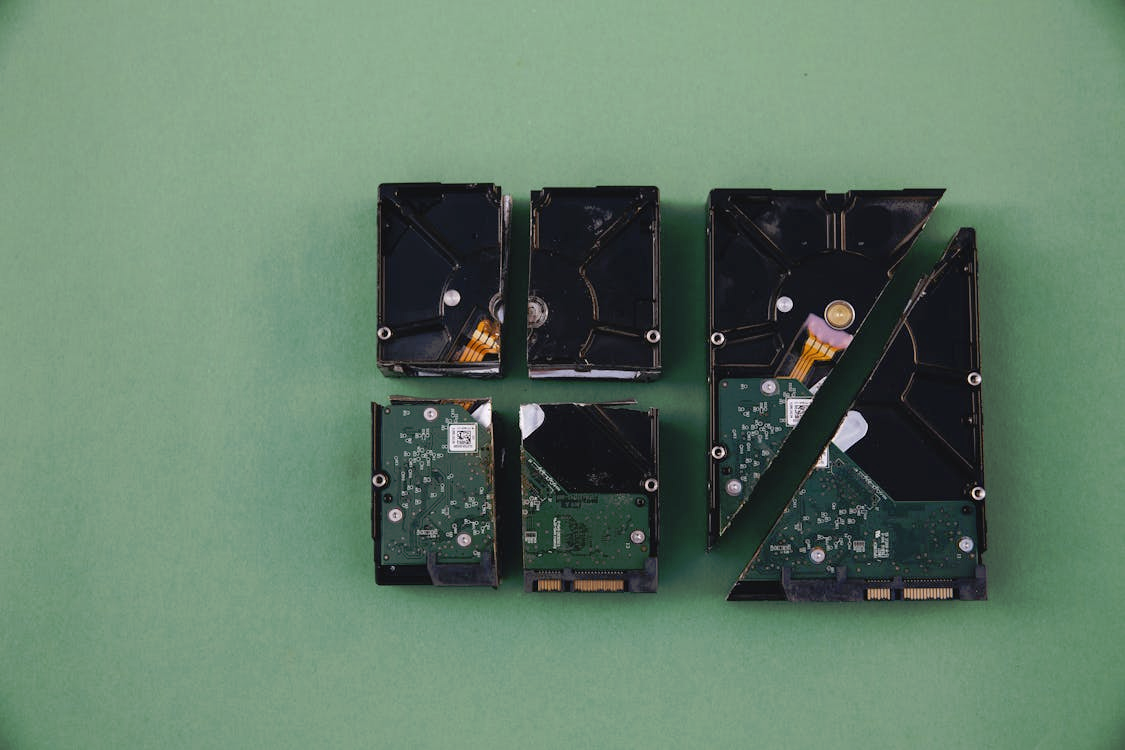
Making data backup seamless is important, and this must apply to mobile devices in addition to fixed hardware. Mobile backups and app data often reveal conversations, location history, and transaction trails. Ignoring them can leave major gaps in evidence. Many investigators focus only on active devices, overlooking synced copies stored in the cloud or on linked computers.
Smartphones constantly replicate data across accounts and services. Collecting those sources early, with consent and proper authorization, preserves a fuller record. Verifying the integrity of mobile backups through forensic imaging helps confirm authenticity and timeline accuracy, reducing challenges to the evidence during trial.
Wrapping Up
Digital evidence demands precision, documentation, and technical consistency. One careless move can compromise an entire case.
Working with trained forensic experts and qualified legal counsel helps ensure every digital artifact stands up in court, keeping the facts clear and defensible from start to finish.

Shikha Negi is a Content Writer at ztudium with expertise in writing and proofreading content. Having created more than 500 articles encompassing a diverse range of educational topics, from breaking news to in-depth analysis and long-form content, Shikha has a deep understanding of emerging trends in business, technology (including AI, blockchain, and the metaverse), and societal shifts, As the author at Sarvgyan News, Shikha has demonstrated expertise in crafting engaging and informative content tailored for various audiences, including students, educators, and professionals.











