Five simple AI defenses stop sophisticated email hacks before they ever reach employee inboxes.Artificial intelligence now powers both sides of the cybersecurity battlefield, allowing attackers to generate flawless phishing lures and easily impersonate executives.
In 2025, phishing-related breaches represented 16 percent of the total security breaches reported.
Defenders who deploy these same intelligent capabilities gain a massive detection advantage over cybercriminals.
They can neutralize complex threats silently and automatically without requiring technical intervention from busy staff.
This shift ensures modern workplaces remain secure while maintaining smooth daily operations.
1. Behavioral Email Analysis Learns Who You Trust
Traditional security rules fail when an attacker uses legitimate-looking credentials to bypass basic network filters.
AI solves this by mapping normal contact patterns, writing styles, file-sharing habits, and send-time rhythms for every user inside an organization.
When an email mimics a trusted sender but deviates in tone or structural context, the system flags it before delivery.
For instance, a CEO impersonation email demanding an urgent wire transfer might pass standard SPF and DKIM checks.
However, it will fail the AI behavioral profile because the communication style is highly irregular compared to normal interactions.
This evolving baseline updates automatically as organizational relationships change over time, requiring no manual policy tuning.
Ultimately, this intelligent protection runs invisibly to ensure employees never have to change how they work.
| Key Insight: Behavioral AI doesn’t just check credentials, it checks context. An email that passes SPF and DKIM will still fail if the writing style, request urgency, or send-time pattern deviates from the established norm. |
2. Predictive Threat Modeling Blocks Attacks Early
Legacy email security relies on a reactive posture, waiting for known signatures to identify a malicious payload.
Predictive threat modeling reframes email defense as a proactive, intelligence-driven operation instead of a waiting game.
By ingesting global threat intelligence and emerging infrastructure patterns, AI identifies malicious campaigns before the first email ever launches.
This intelligence preemptively flags lookalike domains and zero-day phishing infrastructure that attackers spin up using generative models.
Integrating generalized cloud filters, traditional endpoint firewalls, or reliable AI-based email malware protection from Trustifi alongside broader network intelligence feeds helps organizations shift away from emergency patch cycles.
Shrinking the exposure window from days to near-zero catches severe threats that legacy tools miss entirely.
You stop sophisticated attacks your team never saw coming, protecting critical assets around the clock.
This proactive approach neutralizes threats before any lasting damage is done to your network. Your organization effectively stays one step ahead of persistent cybercriminals at all times.
3. Anomaly Detection Spots Subtle Clues You Miss
Human reviewers cannot realistically scrutinize every metadata field of every message they receive throughout the workday.
AI evaluates thousands of email attributes in parallel, surfacing microscopic deviations that are completely invisible to the human eye.
By simultaneously analyzing header construction, attachment behavior, and underlying sending infrastructure, these models detect anomalies instantly.
Because anomaly detection is not signature-based, it catches novel attack patterns and insider threat behavior without needing prior exposure.
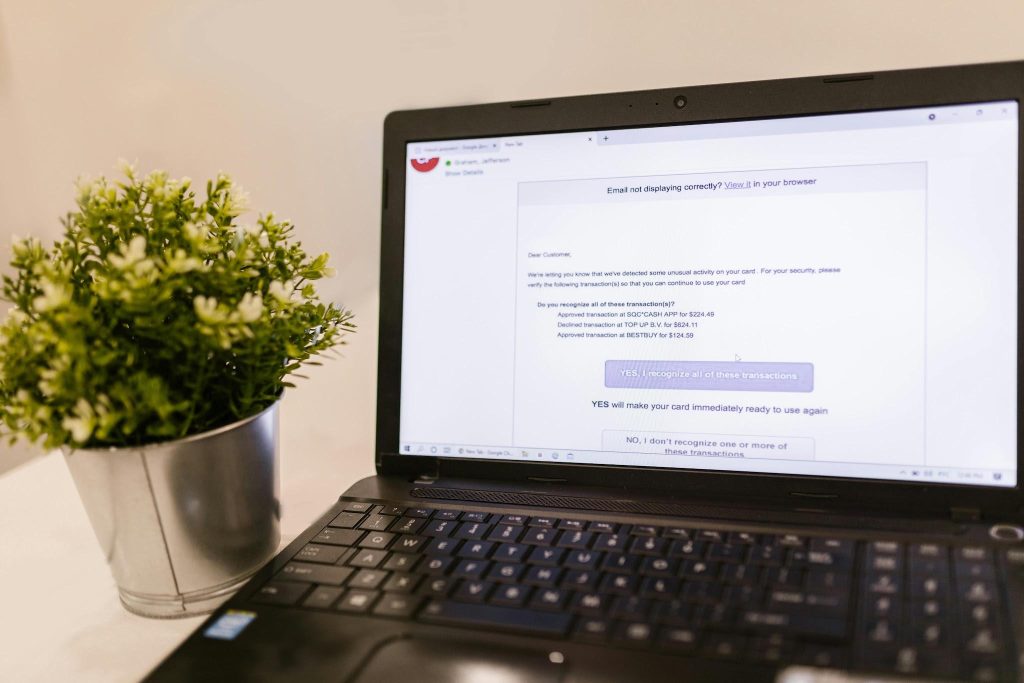
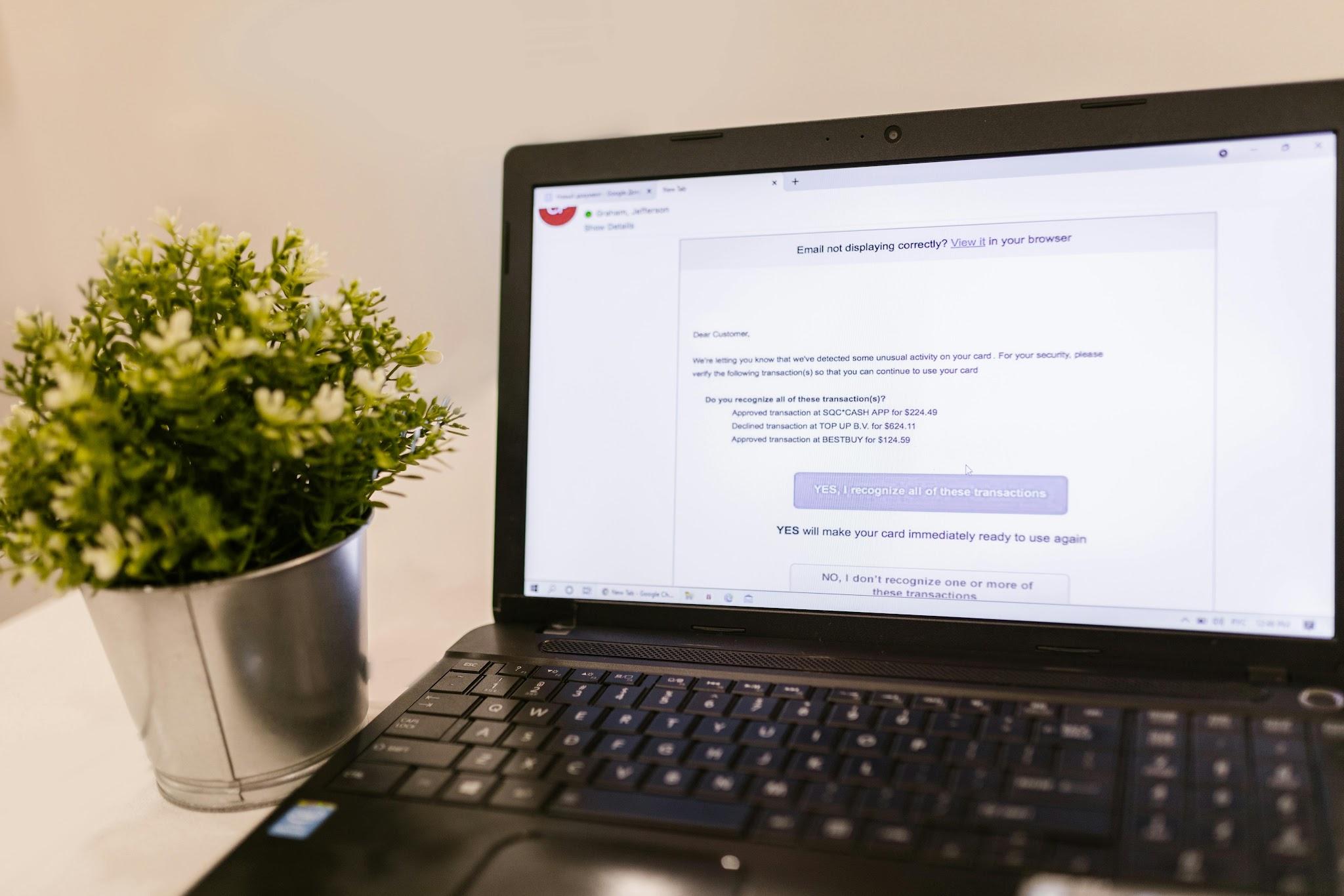
Concrete examples include a forged invoice where the sender’s domain is one character off from the legitimate supplier.
It can also catch a compromised vendor account sending unusual file requests at strange hours.
A quiet data exfiltration attempt disguised as a routine inbox forwarding rule will also trigger an immediate system alert.
At the massive scale your inbox operates, AI consistently catches what limited human attention simply cannot process.
This intelligent and continuous monitoring eliminates alert fatigue for busy IT departments.
4. Automated Response Systems Neutralize Threats Instantly
When seconds separate a safely contained incident from a company-wide data breach, manual remediation workflows are structurally too slow.
Automated response systems act as the critical speed layer that efficiently closes the gap between detection and containment.
Upon confirming a threat, the AI immediately quarantines the malicious payload and retracts already-delivered emails from inboxes.
The system then alerts targeted users, suspends compromised accounts, and seamlessly updates the gateway policy automatically.
This automation serves as a security team’s fastest colleague rather than a workforce replacement.
It handles immediate triage securely so IT staff can focus entirely on broader strategic decisions.
It dramatically reduces the potential blast radius and maintains continuous protection even when staff are offline or overloaded.
With automated containment, your team wakes up to a fully managed incident rather than a chaotic company crisis.
Essential business operations continue running smoothly without experiencing costly network interruptions.
| Important: When seconds count, a manual review queue is a liability. An automated system that instantly retracts delivered emails and suspends compromised accounts contains the blast radius before a single user clicks. |
5. Contextual Content Scanning Understands True Message Intent
Unlike basic keyword filters, contextual content scanning reads emails much like a highly skilled human analyst would.
The AI continuously evaluates tone, urgency, financial language, sender-recipient history, and brand mimicry to understand the actual intent.
It easily distinguishes a routine supplier invoice from a highly forged lookalike registered just days ago.
This intelligence extends naturally to outbound data loss prevention by perfectly understanding broader document context.
The same contextual awareness successfully identifies sensitive data leaving the organization inappropriately.
Real-world examples include protected health information in unencrypted replies or proprietary financial data sent to unverified external addresses.
Platforms that treat inbound and outbound threats as a unified challenge offer seamless convergence to security teams.
Utilizing smart contextual scanners alongside native outbound encryption creates a single, frictionless architecture for modern organizations.
This convergence ensures you catch unauthorized data leaving your organization just as precisely as you block malicious payloads entering it.
| Pro Tip: Unify your defense. The same contextual AI that spots a forged invoice entering your network can identify sensitive data leaving it, closing both inbound and outbound gaps in a single architecture. |
The Road Forward
These five capabilities are actively running inside next-generation security platforms right now, quietly redefining organizational email defense.
Attackers already use artificial intelligence to impersonate executives and generate highly convincing phishing campaigns in a matter of minutes.
They intentionally mutate malware faster than traditional signature databases can respond, making passive security measures obsolete.
The operational asymmetry is real, and the window for relying on traditional filters is rapidly closing.
Defenders who adopt AI-native email security effortlessly shift the advantage back to their side securely.
They operate at a level of speed and intelligence that reactive legacy tools structurally cannot match.
Organizations that embrace AI-powered defense today are not just protecting their daily corporate communications.
They are definitely writing the operational rules that everyone else will eventually be required to follow.
Intelligent cybersecurity remains the absolute foundation for safe, modern business operations moving forward.
| Author Profile: Trustifi is a cloud-based email security platform providing data loss prevention, advanced threat protection, encrypted email communication, and compliance solutions for businesses. |

Founder Dinis Guarda
IntelligentHQ Your New Business Network.
IntelligentHQ is a Business network and an expert source for finance, capital markets and intelligence for thousands of global business professionals, startups, and companies.
We exist at the point of intersection between technology, social media, finance and innovation.
IntelligentHQ leverages innovation and scale of social digital technology, analytics, news, and distribution to create an unparalleled, full digital medium and social business networks spectrum.
IntelligentHQ is working hard, to become a trusted, and indispensable source of business news and analytics, within financial services and its associated supply chains and ecosystems