Hacking The DNA of Humanity with Blockchain and AI
DNA, the famous double helix carrying the genetic instructions used in the growth, development, functioning and reproduction of all living beings, is fundamentally, the critical way of storing the biosphere, and as part of it, all of humanity’s information. It is the foundation of life as we scientifically know it. Conventionally, it gathers and encodes instructions for making living things, but it can be encrypted for other purposes and to evolve according to its organic nature evolutionary programming. Scientists and technologists from all kinds of subjects, as they deepen their understanding of its engineering, are adopting the biological DNA to store what seemed unimaginable some years ago, such as books, recordings, GIFs, and even planning things such as an Amazon gift card.
In a pioneer experiment, Yaniv Erlich and Dina Zielinski, from the New York Genome Center and Columbia University encoded in a single gram of DNA, one of the first films ever made, Lumiere Brothers “The Arrival of a Train at La Ciotat Station” along with a computer operating system, a photo, a scientific paper, a computer virus, and an Amazon gift card.
Their new strategy, was inspired by the codecs that allow movies to stream reliably across the Internet. They were thus able to safely store the digital files into tiny small amounts of DNA.
Blockchain technology and particularly artificial intelligence are directly and indirectly DNA foundational technologies. Somehow, they can be seen as macro concepts of a database, operating in a very similar way to biological DNA. Plus, there are now various experiments using artificial intelligence to manipulate biological DNA. The United States is currently trying to sequence the DNA of at least 1 million Americans to pave the way for precision medicine, which concerns the development of treatments that are specifically adapted to an individual’s genes. As technology and data come to the forefront as the very fabric of our human socio-economic and scientific civilisation, we are faced with new challenges. How can we store and protect our human DNA ? What happens if someone with bad intentions hacks humanity’s DNA?
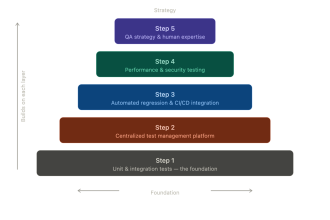
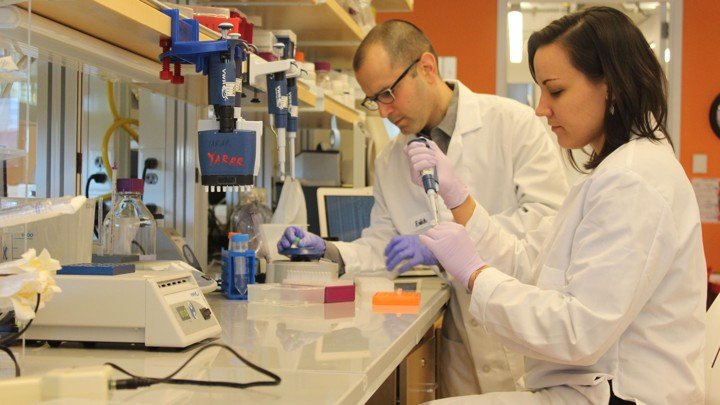
Worldwide, scientists and researchers based in universities and research labs are digitising human and animal DNA at a scale and speed never seen before.But the scientists working at the forefront of these programs don’t tend to consider the dangers of hacking and other breaches in security. There is lack of awareness around best practices for digital security. According to recent surveys, most programs for analyzing DNA have relatively relaxed security standards.Unfortunately, hacking DNA with bad intentions, is now becoming a real risk as certain recents experiments have demonstrated.
In 2017, a team of scientist from the University of Washington managed to take over a computer by encoding malware into a gene and use this to take over a computer program. The team was led by Tadayoshi Kohno, a computer security expert. Kohno and his team has been designing computer security projects for over a decade. In 2008, they worked on another project where they used wireless technology to hack an heart implant, and reprogram it to either shut down or deliver debilitating jolts. Two years later, in 2010, they were able to hack into the control system of a Chevrolet Impala, taking control of the car. More recently they became interested in designing projects concerning DNA sequencing.

Security and Privacy Lab of the University of Washington
In an interview for The Atlantic, Kohno, explains the function of his last project:
“We want to understand and anticipate what the hot new technologies will be over the next 10 to 15 years, to stay one step ahead of the bad guys.”“It’s an emerging field that other security researchers haven’t looked at, so the intrigue was there,” says Kohno. He continues: “Could we compromise a computer system with DNA biomolecules?” “My hope is that over the next 5 to 10 years, people take a strong interest in DNA security, and proactively harden their systems against adversarial threats.”
The experiment worked in the following way: The team introduced a vulnerability into a program that’s commonly used to analyze DNA data files and then exploited that weakness. The team also showed that such vulnerabilities are common in software for analyzing DNA. What they discovered is that it is now possible to steal data, or manipulate it to make it seem like people have genetic diseases they don’t have.
How Can We Secure Humanity’s DNA?
Going forward is cybersecurity, particularly the one involving DNA, the very fabric of human and biological life, the biggest challenge we are currently facing? How can we secure cyber-secure our very own DNA and the one of our society ?
The strands of biological DNA are made from four building blocks, represented by the structures and letters A, C, G, and T. As these letters can be used to represent the 1s and 0s of computer programs this becomes a bigger step toward our very definition of digitalisation and full scale digital transformation of society and human health, life style and socio-economic models. That’s what the scientific Washington research team did—they managed to convert a piece of malware into physical DNA strands.When those structural strands were sequenced, the malware launched and compromised the computer that was analysing the sequences, allowing the team to take control of it and of course, manipulate it. This is a quantum leap into the way we can look at new challenges (and opportunities) coming our of these increasingly complex operations.
The tech for DNA manipulation and precision medicine is for now, at an inception stage, so the threats it poses are still very small. People don’t need to lose sleep immediately, but there is the risk, as the process evolves and the access to more computer power becomes widespread, that people with wrong ethical standpoints, becomes serious can be drawn to use it for ill intentions.
As technologists and scientists using blockchain and AI technology have more advanced knowledge on how to store, safe guard and manipulate big amounts of data and how to relate with global databased, we will have new increasing scenarios of dystopian possibilities but also ways to know what is possible to prevent those possibilities, and what are the issues at stake down the line.
As sequencing becomes a norm, the consequences of DNA manipulation attacks, particularly when done to the data of big groups of humans, organisations or governments, can be more dangerous and severe then ever.
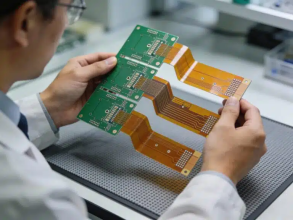
If in the early 2000s, DNA sequencing was extremely costly that is not the case anymore. Back then, just to sequence a single human genome would cost around $100 million USD. Now, you can do it for less than $1,000, plus you can use decentralised systems to do so. The technology, is not only cheaper, but also simpler and movable. This means that you can analyze DNA not only in space stations, but in classrooms, and all kinds of different locations. So technologists’s different ethical characteristics according to location, culture, interests are more relevant then ever.

MiniION is a portable DNA sequencer
We are living early and disruptive days. The last decades have brought with digitisation a somehow darkenisation of the web technology – internet. The possibilities of what can be done augment, particularly due to the recent invention of blockchain smart contract tech, machine learning and advance swarm intelligence.Swarm intelligence is a concept first introduced by Gerardo Beni and Jing Wang, in 1989, in the context of cellular robotic systems. The greatest possibilities implicit in these ubiquitous technologies, rise the greatest of the vulnerabilities: the possibility of hacking/manipulating, humanity’s code.
Biological DNA in the history of humanity and science is still a recent and quite underdeveloped technology, resulting from mostly a few decades of scientific research. For now it is commonly used just in selected areas. But as I said previously, with the new advancements in computer power and AI, if less ethical people – with totalitarian view points or ill intentions, take interest in using it to do harm, it can be very dangerous. Possible scenarios include hacking sequencing machines, entire hospital databases or even country health care records. In this scenario, it would be possible to alter the genetic data of an entire group or society. Bearing in mind that Nazis used early stage IBM computers to kill Jews during the second world war unfortunately we need to be prepared to some hard core scenarios. Other dystopian scenarios, include machines that evolve faster than expected and start collaborating and influencing different decisions such as enabling the processing of confidential data about genetically modified organisms, or hackers that could steal intellectual property or manipulate systems of data and decisions.
The future Humanity will be about evolutionary organic swarm intelligence and blockchain combined with artificial intelligence machine learning data related systems. How to apply these technologies to health, society, financial systems and economic models in the best possible ways, preventing the vulnerabilities cited previously ? In order to make it work for the common good, key players such as technologists, governments and regulatory boards, will need to create an infrastructure of solid systems of peer-to-peer networks, underlying operations based in strong governance and ethics. These, need to be managed in a wise way, according to decentralised or distributed systems of standards, which follow global protocols. An example of this, would be the registering all human identity(ies) in distributed ledgers run by smart contracts and operating in an integrated way, with holistic machine learning enabled by IoT devices and sensors.
This needs to be done, I repeat, in a trustworthy way, anchored in a solid system of global standards. Otherwise we might fall into a science fiction dystopian scenario, which is difficult to predict, as it is the result of a series of black swan innuendo waves, triggering the potential next tsunami.
Author

Dinis Guarda is an author, academic, influencer, serial entrepreneur, and leader in 4IR, AI, Fintech, digital transformation, and Blockchain. Dinis has created various companies such as Ztudium tech platform; founder of global digital platform directory businessabc.net; digital transformation platform to empower, guide and index cities citiesabc.com and fashion technology platform fashionabc.org. He is also the publisher of intelligenthq.com, hedgethink.com and tradersdna.com. He has been working with the likes of UN / UNITAR, UNESCO, European Space Agency, Davos WEF, Philips, Saxo Bank, Mastercard, Barclays, and governments all over the world.
With over two decades of experience in international business, C-level positions, and digital transformation, Dinis has worked with new tech, cryptocurrencies, driven ICOs, regulation, compliance, and legal international processes, and has created a bank, and been involved in the inception of some of the top 100 digital currencies.
He creates and helps build ventures focused on global growth, 360 digital strategies, sustainable innovation, Blockchain, Fintech, AI and new emerging business models such as ICOs / tokenomics.
Dinis is the founder/CEO of ztudium that manages blocksdna / lifesdna. These products and platforms offer multiple AI P2P, fintech, blockchain, search engine and PaaS solutions in consumer wellness healthcare and life style with a global team of experts and universities.
He is the founder of coinsdna a new swiss regulated, Swiss based, institutional grade token and cryptocurrencies blockchain exchange. He is founder of DragonBloc a blockchain, AI, Fintech fund and co-founder of Freedomee project.
Dinis is the author of various books. He has published different books such "4IR AI Blockchain Fintech IoT Reinventing a Nation", "How Businesses and Governments can Prosper with Fintech, Blockchain and AI?”, also the bigger case study and book (400 pages) “Blockchain, AI and Crypto Economics - The Next Tsunami?” last the “Tokenomics and ICOs - How to be good at the new digital world of finance / Crypto” was launched in 2018.
Some of the companies Dinis created or has been involved have reached over 1 USD billions in valuation. Dinis has advised and was responsible for some top financial organisations, 100 cryptocurrencies worldwide and Fortune 500 companies.
Dinis is involved as a strategist, board member and advisor with the payments, lifestyle, blockchain reward community app Glance technologies, for whom he built the blockchain messaging / payment / loyalty software Blockimpact, the seminal Hyperloop Transportations project, Kora, and blockchain cybersecurity Privus.
He is listed in various global fintech, blockchain, AI, social media industry top lists as an influencer in position top 10/20 within 100 rankings: such as Top People In Blockchain | Cointelegraph https://top.cointelegraph.com/ and https://cryptoweekly.co/100/ .
Between 2014 and 2015 he was involved in creating a fabbanking.com a digital bank between Asia and Africa as Chief Commercial Officer and Marketing Officer responsible for all legal, tech and business development. Between 2009 and 2010 he was the founder of one of the world first fintech, social trading platforms tradingfloor.com for Saxo Bank.
He is a shareholder of the fintech social money transfer app Moneymailme and math edutech gamification children’s app Gozoa.
He has been a lecturer at Copenhagen Business School, Groupe INSEEC/Monaco University and other leading world universities.